We are excited to announce a new capability in the Upwind platform, providing organizations with deep visibility into Kubernetes’ ingress traffic to identify exposures and risks.
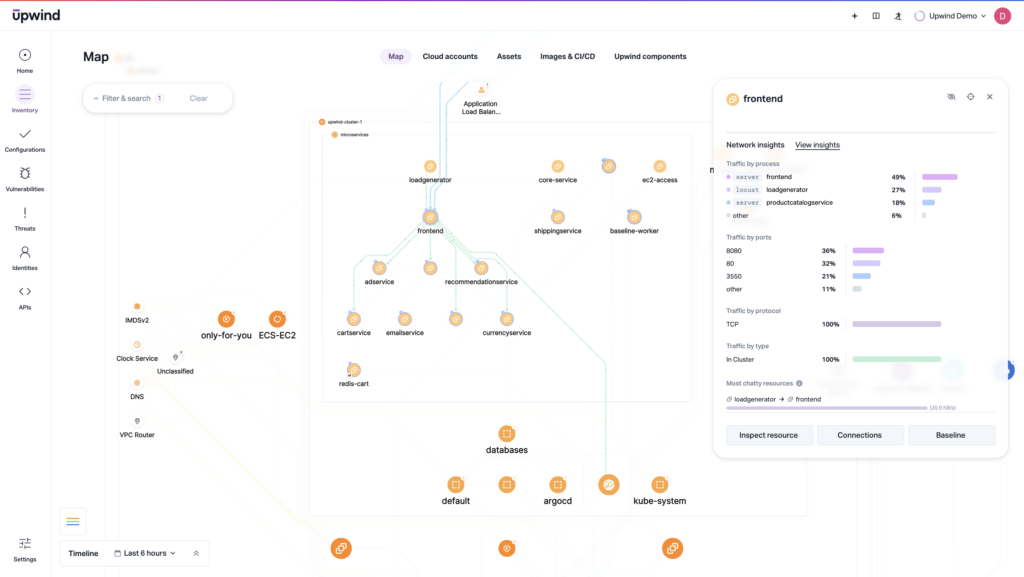
Traditional security systems often fall short in providing comprehensive visibility into how Kubernetes ingress services distribute incoming internet traffic within a cluster, leaving potential blind spots that malicious actors could exploit. Upwind solves this challenge by automatically discovering transient ingress traffic and showing the entire ingress communication path on the Upwind Topology Map – a capability that goes beyond traditional security tools, which often fail to provide real-time mapping of ingress service exposures. This empowers organizations to understand ingress service risks with greater clarity and take proactive security measures.
What is Kubernetes Ingress?
Kubernetes Ingress is an API object that manages external access to services in a cluster. It is typically HTTP, and may provide load balancing, SSL termination and name-based virtual hosting.
In practice, Ingress exposes HTTP and HTTPS routes from outside the cluster to services within the cluster.
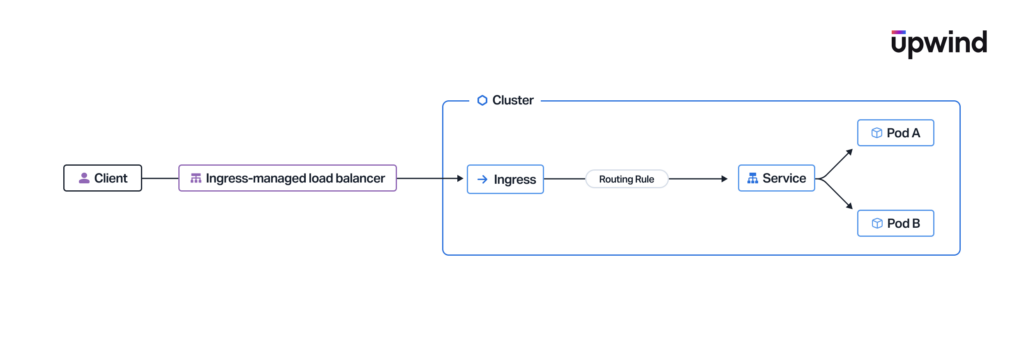
Ingress services in cloud environments act as gateways, directing external traffic to internal services. While it’s essential to monitor these entry points, traditional security tools often lack the depth to trace the path of this traffic beyond the ingress point. This limitation means that once traffic enters the cluster, its path remains obscured, making it difficult to assess which internal resources are exposed to external threats. These gaps in visibility can lead to undetected vulnerabilities, as any service communicating with an ingress point could potentially be at risk. For example, in past incidents, misconfigured ingress controllers have inadvertently exposed internal databases or authentication services to the internet, leading to unauthorized access and data breaches. Without a clear view of ingress traffic paths, security teams may struggle to detect these exposures before they are exploited.
How Upwind Provides Visibility into Kubernetes Ingress
With this new release, organizations can view the entire Kubernetes ingress communication path from Kubernetes Ingress to specific services within a cluster. By mapping out the entire communication path, Upwind enables security teams to see beyond the ingress point, identifying all internal services that interact with external data.
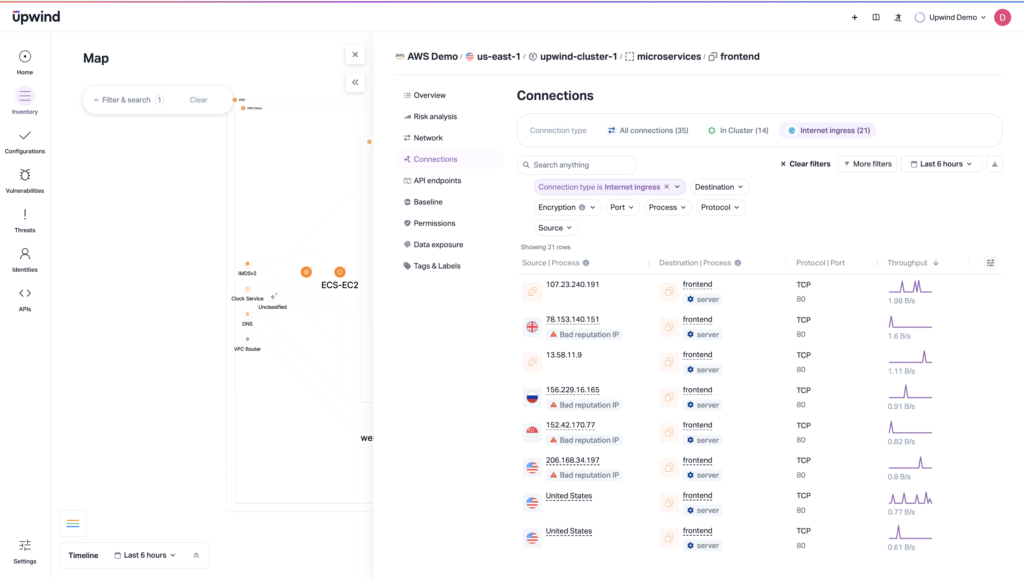
In practice, any resource that receives Kubernetes Ingress traffic is at increased risk because of its communication with the Internet. Along with tracing the entire communication path, Upwind also correlates the Ingress communication risk with additional risk factors, including:
- Resources with Ingress traffic that also contain vulnerabilities that are exploitable and have a fix available
- Highly-privileged identities that have access to resources with Ingress communication, including:
- Cloud IAM High-Privilege Roles
- Kubernetes High-Privilege Roles
- Kubernetes Security Context
- Pivot to Cloud – K8s Resources with Cloud Permissions
- Resources with Ingress traffic that also contain sensitive data, including:
- PHI data: patient information, medical records & insurance information
- PII data: SSNs, IDs and emails
- PCI data: credit cards and billing information
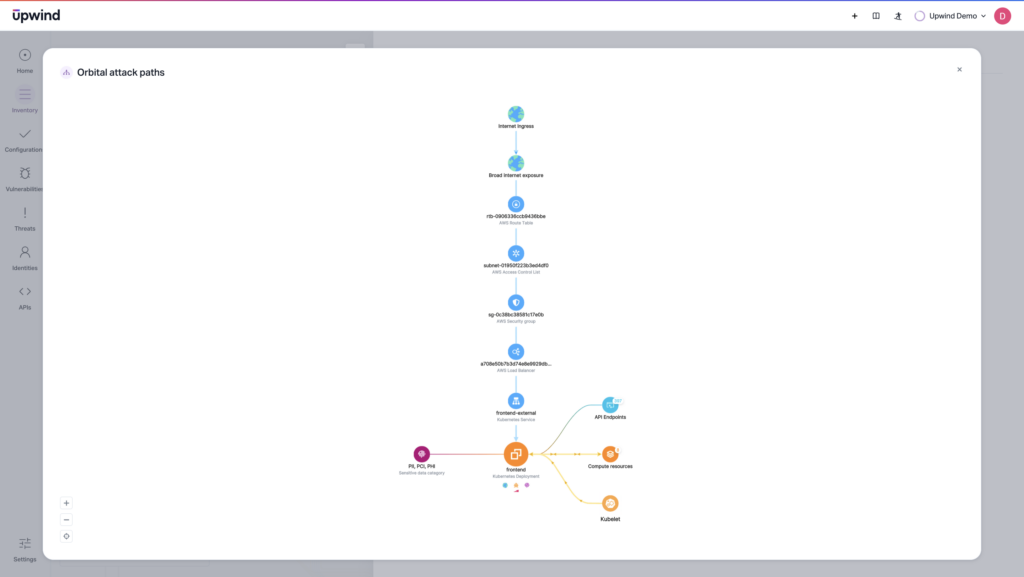
By tracing the Kubernetes Ingress communication path throughout the cluster, Upwind empowers organizations to gain increased visibility into their resource behaviors, understand service communication with the Internet, and identify exposed resources. This enhanced visibility enables security teams to respond to incidents faster, proactively mitigate risks, and implement more precise access controls, reducing the likelihood of ingress-related breaches. Upwind’s deep awareness enables organizations to prioritize at-risk resources, focusing on resources with Ingress communication that are exposed to an open attack path.
Learn More
Upwind’s ability to visualize Kubernetes Ingress communication paths empowers organizations to uncover hidden exposures, assess risks accurately, and prioritize exposed vulnerabilities for remediation. With an intuitive interface, security teams can quickly access ingress communication insights through the Upwind platform, making it easy to navigate risk assessments and take immediate action.By providing this deep visibility and runtime context, Upwind helps organizations enact proactive security measures and prioritize their most critical risks. To learn more about how Upwind empowers organizations with Kubernetes Ingress visibility and deep risk prioritization, schedule a demo today.